Newsletter #013: Large Phishing Operations Against Maintainers 🎯
Written by Ulises Gascón
Apr 07, 2026 — 11 min readThis post was originally shared with my GitHub Sponsors. If you'd like to get early access to updates like this and support my open source work, consider becoming a sponsor here. 🙌
Hola everyone! 🎉
Hope you've all been doing awesome since our last catch-up. This one's heavy. A coordinated phishing campaign hit close to home, targeting maintainers across the ecosystem. Including myself. But there's also good news to share, so let's not start on a dark note.
Let's dive in! ✨
🛡️ Maintainers Under Attack: The Axios Supply Chain Compromise
On March 31, two malicious versions of axios (1.14.1 and 0.30.4) were published to npm through a compromised maintainer account. The attacker injected a dependency that installed a remote access trojan on macOS, Windows, and Linux. The malicious versions were live for about 3 hours before being removed.
But the real story is bigger than axios. This was a coordinated, multi-week social engineering campaign targeting high-impact open source maintainers. The tactics match what appears to be a well-resourced state actor operation that has been using this playbook against cryptocurrency and venture capital targets since at least 2018. The playbook: fake company personas reaching out via LinkedIn or Slack, building rapport, scheduling video calls on spoofed platforms, and tricking maintainers into running malware through a fake "audio failure" prompt.
The list of people targeted includes maintainers of some of the most critical packages in the ecosystem: axios, Express, Lodash, Fastify, Undici, dotenv, WebTorrent, StandardJS, and many others. Including myself.
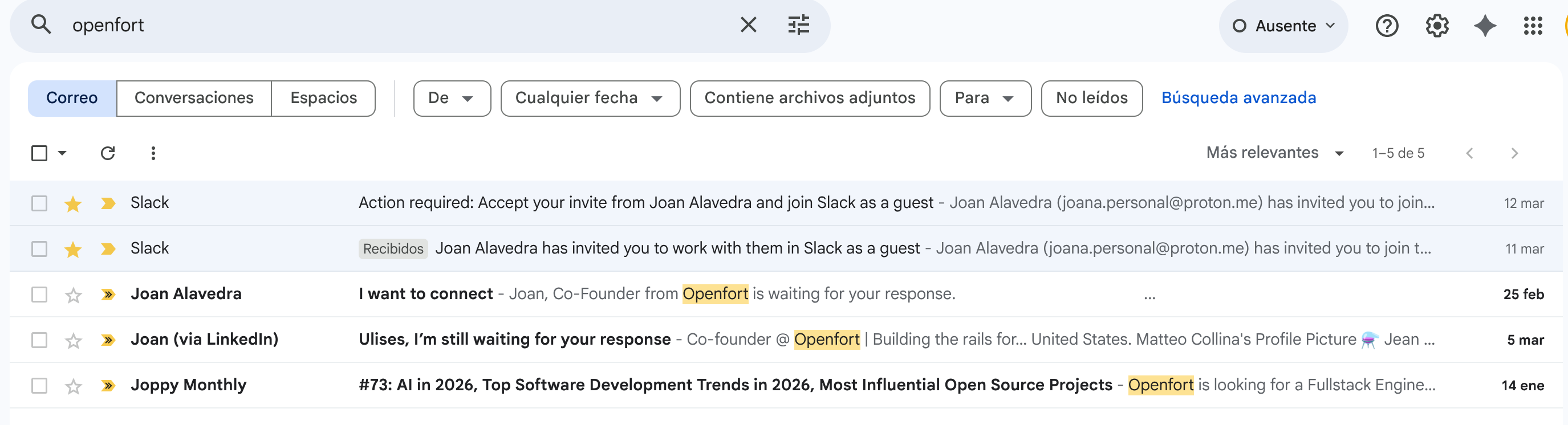
I was also targeted. Lucky that it takes me years to check my inbox 💀
Since the XZ incident, and now with LLM capabilities making social engineering easier to scale, the pressure on open source maintainers keeps growing. As Sarah Gooding put it:
Open source maintainers are high-value targets. Supporting them requires more than better tooling or stricter controls. It requires treating maintainers as critical infrastructure themselves, with the time, boundaries, and support systems needed to sustain that role.
2FA doesn't help once malware is on the machine. OIDC-based publishing doesn't prevent compromise of a fully infected system. Awareness and transparency help, but they're not enough. We need to start recognizing maintainers as critical infrastructure and provide the institutional and operational support to match the responsibility we already carry.
In the backstage, the OpenJS Security Working Group played a key role connecting the dots across projects and coordinating the response. That's exactly the kind of structure that makes a difference when things go wrong. Huge thanks to the Socket team for the fast and thorough coverage that helped the community understand the full scope of the campaign.
✅ Scorecard v6: From Scoring Tool to Security Evidence Engine
Scorecard v6 is taking shape, and this is a big evolution. The project is moving from being a scoring tool to becoming an open source security evidence engine.
The key idea: Scorecard will produce trusted, structured security evidence that downstream tools can act on. It accepts diverse inputs about a project's security practices, normalizes them through probe-based analysis, and packages the results in interoperable formats. Check scores (0-10) and conformance labels (PASS/FAIL/UNKNOWN) become parallel evaluation layers over the same probe evidence. Existing checks, scores, and output formats are preserved.
The primary initiative for 2026 is adding OSPS Baseline conformance evaluation as the first use case. This means Scorecard can now tell you not just "how secure does this project look" but "does this project meet a defined security baseline." We've also published a dependency-ordered implementation plan for Phase 1.
Downstream tools like scorecard-monitor and scorecard-visualizer will also need to evolve to support the new conformance layer and output formats.
🎤 Most Developers Misunderstand Node.js in Production
I had the chance to join NodeSource's "Beyond Node.js" series for a conversation about what most developers get wrong about Node.js in production.
We talked about common misconceptions, production patterns that look fine in development but break under real load, and how error handling actually works. If you're interested, check out Rafael Gonzaga's episode too.
📦 Release Backlog Updates
Here is what I released recently:
🔐 Security Updates
This has been a busy period on the security front. We triaged and patched 12 CVEs across multiple projects, and we also kicked off the Express.js monthly security newsletter to keep the community informed.
undici
- CVE-2026-2229 — Medium-severity. Unhandled exception in WebSocket client due to invalid
server_max_window_bitsvalidation (GHSA-v9p9-hfj2-hcw8) - CVE-2026-1526 — Medium-severity. Unbounded memory consumption in WebSocket permessage-deflate decompression (GHSA-vrm6-8vpv-qv8q)
- CVE-2026-1527 — Medium-severity. CRLF injection via
upgradeoption (GHSA-4992-7rv2-5pvq) - CVE-2026-1528 — Medium-severity. Malicious WebSocket 64-bit length overflows parser and crashes the client (GHSA-f269-vfmq-vjvj)
- CVE-2026-1525 — Medium-severity. HTTP request/response smuggling (GHSA-2mjp-6q6p-2qxm)
- CVE-2026-2581 — Medium-severity. Unbounded memory consumption in DeduplicationHandler via response buffering (GHSA-phc3-fgpg-7m6h)
fastify
- CVE-2026-3635 — Medium-severity.
request.protocolandrequest.hostspoofable viaX-Forwarded-Proto/Hostwhen trustProxy uses restrictive trust function (GHSA-444r-cwp2-x5xf)
path-to-regexp
- CVE-2026-4867 — High-severity. ReDoS via multiple route parameters (GHSA-37ch-88jc-xwx2)
- CVE-2026-4926 — High-severity. Denial of Service via sequential optional groups (GHSA-j3q9-mxjg-w52f)
- CVE-2026-4923 — Medium-severity. ReDoS via multiple wildcards (GHSA-27v5-c462-wpq7)
lodash
- CVE-2026-4800 — High-severity. Code injection via
_.templateimport key names (GHSA-r5fr-rjxr-66jc) - CVE-2026-2950 — Medium-severity. Prototype pollution via array path bypass in
_.unsetand_.omit(GHSA-f23m-r3pf-42rh)
📚 What Else?
The Node.js Security Bug Bounty Program has been paused due to loss of funding. This is a tough one. The program was a meaningful incentive for external researchers to report vulnerabilities responsibly, and without it there's a real risk that high-quality findings get distributed underground instead. That's exactly why these programs exist in the first place.
It's also worth mentioning that bounty rewards mostly go to reporters. Under the IBB model, fixers only see 20% of the payout, and in most of the ecosystem, that work remains volunteer effort.
On a related note, we recently introduced a Signal requirement on HackerOne as we covered in the last issue, and now we're exploring LLM-assisted triage to further reduce the noise. AI-generated reports are a growing problem, and having better tooling to filter signal from slop will be critical whether or not the bounty program returns.
The Node.js release schedule is now official. This has been in the works for a while, and it's great to see it formalized. Clearer expectations for everyone involved.
The Temporal date-time API has reached Stage 4 at TC39. After years of work, this is a major milestone for the JavaScript ecosystem. Already testing it in the console:
const now = Temporal.Now.plainDateTimeISO()
const meeting = Temporal.PlainDateTime.from('2026-04-07T15:00:00')
const duration = now.until(meeting)
console.log(`Meeting in ${duration.hours} hours and ${duration.minutes} minutes`)
// Meeting in 0 hours and -32 minutes
Late to my own meeting, but at least the API works 😅, jokes aside you can test this already on Chrome and many other platforms.
On the Lodash front, we shipped the first minor release since the security reset and, for the first time, published individual packages too. There's also a CVEs refresh on the way to make sure the advisory data stays accurate across the new package structure.
I migrated and updated the npm Ecosystem Impact report. If you're a sponsor, this is a great way to see how your support is making a real impact across the ecosystem.
I opened a PR to bring express-session towards RFC 6265 compliance. The previous path matching used a simple prefix check, which meant /admin would incorrectly match /administrator. The fix implements proper segment-boundary-aware matching as defined in the spec.
The OpenJS Foundation published a piece on burnout among open source maintainers, featuring a conversation with John-David Dalton, creator of Lodash. There's also a video version worth watching. This is a topic that doesn't get enough honest attention, and it's one we need to keep talking about.
Jordan Harband was interviewed on Harper (S4 E6) about his experience maintaining 500+ npm packages, his work on TC39, and how he balances open source with family life. A lot of interesting ideas on finding a good life balance as a maintainer.
T3chFest is one of my favorite tech events in Spain, and they are gradually releasing the recorded talks from this year's edition. I had the pleasure of speaking there a few years back (Scraping épico para gente sin APIs, AireMad y el Open Source). Keep an eye on their channel.
🎖️ Awesome People Doing Awesome Things
Robin Bender Ginn, Executive Director of the OpenJS Foundation, presented "The Real Supply Chain Risk: Unsupported Dependencies, Overloaded Maintainers" at RSAC 2026. Her core argument connects directly to what this issue covers: open source risk is not just a function of vulnerabilities, it's a function of whether the project has the capacity to respond to them. The phishing campaign, the bounty pause, the burnout conversation. They all point to the same structural problem. A much-needed message at the right stage.
Fun fact: back in 2020, Robin interviewed NASA astronaut Christina H. Koch at an OpenJS Foundation keynote. This week, Koch and the rest of the Artemis II crew became the humans who have traveled the farthest from Earth in history, reaching 252,756 miles during their lunar flyby 🚀
Paulo Matos built JSSE, a JavaScript engine created entirely by an AI agent. A fascinating experiment to learn about AI-assisted development and when it makes sense to go full YOLO mode. Check out the full write-up. Thanks to it I also discovered ccusage, a tool to track token usage and translate these kind of efforts into actual costs. In the last issue I mentioned how AI is helping me explore ideas like lodash-benchmarks that I would normally say no to because it means deprioritizing other work. Paulo's experiment is a great example of that same strategy: using AI to open exploration opportunities that wouldn't exist otherwise.
Javier Sáez Gallego launched GeoFiles, a tool for working with geospatial data in the cloud. Love the passion for indie projects connected to geospatial data!
Seth Larson and Mike Fiedler did an excellent job with the incident response on the PyPI litellm/telnyx supply chain attack. Fast, transparent, and thorough. Supply chain attacks are not exclusive to npm, and seeing this level of coordination across ecosystems is encouraging. The Python Software Foundation (PSF) has been making a great investment in improving their security posture, and it shows. Check out their 2025 year in review to see the full journey.
Pelle Wessman has been doing great work on CWE filters. Thanks to him spotting a bug, I improved my RSS feed to be more discoverable. Considering that most of my time recently has been dedicated to security work, Pelle is right to point out that my feed is starting to look like a CVEs and releases timeline 😅 his suggestion about building dedicated feeds for security and releases is something I'm seriously considering.
César from La Hora Maker put together a thoughtful recap on the AI/LLM landscape. AI tooling has evolved a lot recently, and it can be hard to keep up with all the new ideas, features, and ways to use it. This video covers that gap from a very pragmatic and thoughtful perspective. Great if you missed the last two years of small jumps.
Joyee Cheung developed the fix for the March 2026 Node.js HashDoS vulnerability (CVE-2026-21717). A crafted JSON payload of just ~2 MB could hang a server for ~30 seconds by exploiting deterministic hash collisions in V8's string table. The fix introduced a seeded xorshift-multiply hash with zero performance impact. Great coordination across Node.js, V8, Deno, and Cloudflare Workers to ship it in parallel. The write-up is an amazing deep dive into many internals and a great opportunity to understand how security bugs can appear across the many layers that make up Node.js.
🔗 Interesting Stuff
Some awesome reads from my network:
- Glama | Open Source Has a Bot Problem
- Addy Osmani | Comprehension Debt - the hidden cost of AI generated code.
- Jimmy Vo | A Review of Claude Cowork Virtualization
- Ayende | The Million AI Monkeys Hypothesis: Real-World Projects
🙌 Thank You!
As always, your support as a sponsor makes all of this possible 💖
Whether you're contributing code, giving feedback, or just following along. Thank you!
Stay awesome, Ulises Gascón